By Olivia Cahoon
The Internet of Things (IoT) networks physical devices through embedded software, enabling a data exchange as well as remote access.
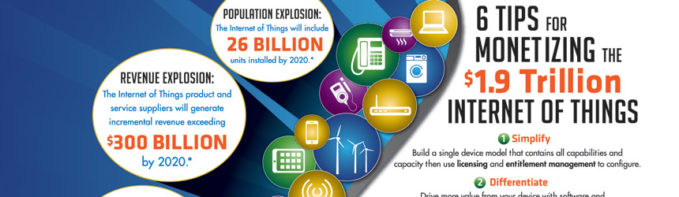
With increased interest in IoT, independent software vendors (ISVs) require a strategy to protect intellectual property (IP). Despite the threat of security breaches, ISVs still capitalize on the IoT. In this article, we look at the qualities surrounding software monetization offered by ISVs for the IoT.
A variety of solutions are available to aid in IP protection specific to IoT, offering tools for IP monetization, manufacturing control, inventory management, system integrity, anti-counterfeiting, and connectivity.
Software in the IoT
The IoT is steadily increasing. As more devices become connected, demands for lower prices, faster products, and more flexible licensing models and product configurations emerge. Software monetization tools are available to protect the IP of those investing in the IoT.
Eric Free, strategic growth senior VP, Flexera Software, says device manufacturers realize the value of software, and that a physical device’s value is defined by the embedded software.
“As manufacturers move towards the IoT and connected solutions, they begin to leverage software within different layers of their solutions,” says Free. Large business opportunities for ISVs offering IoT solutions are created from software applications, cloud solutions management, and data reports.
The extraction of data and the manner in which it is used is a valuable feature of IoT software. Devices connected to the IoT provide exuberant amounts of data. Brendan O’Brien, co-founder/CIO, Aria Systems, explains that the extraction of valuable data has market potential. Software monetization ensures that data is desirably measured and monetized.
IoT software also provides ease of use. Marcellus Buchheit, CEO/president, Wibu Systems, points out enhanced features built into software are more easily and cost effectively upgraded than electronics and mechanics.
IoT Combats Challenges
The IoT provides many benefits, but also comes with security risks. Software vendors look for tools designed for monetization within this field, offering solutions for IP protection, software commoditization, interoperability, and licensing challenges.
Todd Steel, software monetization products director, Gemalto, cites a recent survey, Software Licensing: Expectations, Challenges, and the Future, found 84 percent of IoT software vendors and enterprise end users worry about software comprise. Gemalto commissioned Vanson Bourne to undertake the research for the report.
Software is often supported on many devices to reduce the risk of compromise. “Instead of creating numerous versions of a certain software application, ISVs develop one full software program and use software monetization to activate the features or licenses request,” says Steel. The program reduces development and management costs.
Security reassurance is a priority for those concerned with delivering secure applications and the capability to provide fast updates. “ISVs need to build secure, tamper-resistant applications, and security measures should be applied at all layers of the device’s firmware and software,” adds Free.
Protecting personal information and maintaining uptime are an ongoing challenge. O’Brien relates these problems to the cyberattacks experienced by Democratic National Party and DYN servers. “Building an enterprise-grade vendor means proactively taking actions to reduce risks while also providing a secure and available system for clients,” he says.
ISVs Capitalize on the IOT
With demands for data extraction and combatting security risks, ISVs produce IoT monetization software simplt and customable.
ISVs capitalize on the IoT by gathering telemetry and usage data from the large amounts of captured data. “There is a growing need for analytics and reporting applications, as well as mobile applications and Software as a Service solutions that show results created from this data back to the end users,” says Free. Applications are built on top of IoT platforms to serve value-added services to customers.
ISVs also use the IoT to create customizable programs. O’Brien uses Netflix as a prime example. Netflix is a customizable streaming TV process that uses data to predict what subscribers would like to watch based off their viewing history and tracks where they paused shows, which is shared and updated on all devices. It is a simple form of streaming that delivers ease of use.
To profit money in the IoT, O’Brien warns not to look at the device’s selling margin, but rather at the potential for paid and perpetual recurring services unlocked by the device. He adds that consumer and industrial sectors have recently been disrupted by recurring revenue models.
“A recent Gemalto software monetization survey, Software Licensing: Expectations, Challenges, and the Future, found that 70 percent of respondents agree that the IoT could provide their organization with new monetization opportunities,” cites Steel. He predicts the opportunity will come with the growth of software consumption beyond just enterprises and from consumers too. The opportunities for ISVs to include value-added services to software packages are immense.
Protecting Intellectual Property
ISVs should still be cautious when approaching IoT relationships to protect IP. Free says protecting IP is one of the core initiatives for software vendors as they approach new markets and plan to derive more value from their products. ISVs do this by implementing licensing to help customers manage entitlements so that only eligible customers access the software.
Free says customers should also track software usage, implement a call-home compliance functionality, create tamper-resistant applications to deter hacking, implement self-updating capabilities, and manage OSS usage and all implications on licensing and IP rights.
Buchheit believes that IoT devices follow the evolution of PCs and cellphones and are built with an open architecture utilizing standardized operating systems. The open architecture exposes vulnerabilities to be exploited by hackers, and ISVs have the challenge of implementing security mechanisms to prevent license copying and to enable secure license transfer online.
Steele says other security issues with IP theft in the IoT environment include software piracy, reversing engineering, trade secret theft, code tampering, and gray market activity. Gray market activity is selling or importing devices outside of the usual distribution channel identified by the manufacturer. “Gray markets hurt companies like device markers and ISVs by undermining segmented pricing schemes, causing damage to channel relationships, reputation, and brand loyalty,” adds Steel.
Platforms in the Market
Aria Systems has a cloud-based monetization platform to give existing customers fresh techniques for consuming products and services. “We call it multi-dimensional customer choice that allows customers to buy what they want, when they want it, and how they want it,” says O’Brien.
The customer choice technique extends to offer packaging, customized bundles, and promotions. O’Brien explains that Aria Systems helps process consumption data to give an unprecedented view into customer behaviors and usage patterns. He adds, “With these insights, you can provide perfectly timed, spot-on offers and incentives that customers relish as you furnish the personalized attention they’ll reward over and over again.”
FlexNet Licensing powers Flexera Software Solutions for compliance with software monetization models. Its solutions include FlexNet Operations to manage customer entitlements and FlexNet Connect to provide automated software and firmware update solutions. Free says the Flexera software monetization platform is used by over 3,000 software vendors and intelligent device manufacturers in over 20,000 FlexEnabled applications. “These solutions provide critical business intelligence to sense market change, develop the appropriate course corrections, and deliver the flexibility to quickly adapt to evolving business needs,” explains Free.
The Flexera software monetization includes entitlement management, electronic software delivery, software licensing and updates, compliance management, and extensive consulting.
Gemalto has more than ten years in the IoT or machine-to-machine space and 30 years in software monetization. Gemalto’s software monetization business highlights its family of security, protection, licensing, usage, and entitlement services. The Gemalto Sentinel product line supports a connected and disconnected environment with a back office management system. “It is unique in supporting companies who are still interested in maintaining a non-IoT offering while exploring an IoT offering for specific lines of their products,” says Steel.
Wibu Systems offers CodeMeter licensing and protection platforms for PC software and embedded software utilized in IoT devices. The platform supports secure license storage on physical devices like USBs, internal USBs, SD cards, microSD cards, CF cards, and ASIC form factors. It also supports file-based license activation. “CodeMeter offers secure, flexible licensing options to help ISVs monetize software, such as time-based licensing, subscription-based, pay-per-use licensing, and feature-on-demand licensing,” says Buchheit.
The software provides security between the license and software, and it encrypts the license file during activation. CodeMeter protects IP with AES encryption and by encrypting specific features and functions.
Driving Markets
Countless industries tap into the IoT. According to a whitepaper by GreyHeron, commissioned by Gemalto, Monetizing the IoT: Show Me the Money, the ten top areas driving the IoT ecosystem include quantified self ehealthcare, connected homes; smart buildings, lights, and security; industrial internet, agriculture 2,0; smart cities and eGovernment; utilizes and energy grids; retail stores; smart cars; and intelligent transportation.
Here, we profile PolySync, a technology company that helps shape the future of driverless vehicles. The company searched for an IoT monetization solution when it realized too much time was spent on the back-end infrastructure software for its IoT vehicle system. Before the company designed a centralized platform, the software for autonomous vehicles was incompatible so that companies were forced to do back-end coding.
PolySync needed a software licensing and entitlement management system capable of meeting increased demand that automated software delivery with updates and enabled product differentiation to pursue opportunities. It also needed a flexible software licensing and entitlement management system to accommodate a growing customer base.
The company’s founders launched PolySync software to eliminate inefficiency on a software platform that manufacturers use to control device sensors, communications, and control systems.
PolySync approached Flexera and implemented FlexNet Licensing for protection of IP, FlexNet Connect for automated updates, and FlexNet Operations to manage licenses. Flexera’s software monetization allowed PolySync to license PolySync software to customers and provide nonstop customer self-service for managing the software license lifecycle.
The company’s autonomy operating system, PolySync software, is a software platform designed to help developers build, test, and deploy driverless vehicle applications. The company chose Flexera for flexibility, scalability, and credibility. “PolySync recognized that Flexera Software offered a broad range of interoperability with different platforms, operating systems, and API’s. The technical flexibility was key,” says Free.
Software Monetization
ISVs play an important role in the IoT. In addition to driving intelligence, customer data is extracted and utilized to its full potential. As more devices become connected to IoT, the opportunities for ISVs increase as do the challenges. Security breaches are a concern for companies who want to protect IP. Luckily, several software monetization and license management tools are available to support ISVs in IoT environments.
Feb2017, Software Magazine